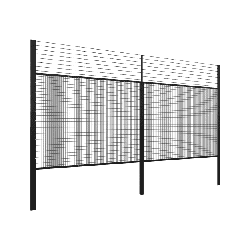
Exclusion Zone Security Fencing
Sometimes one fence just isn’t enough. This is especially true when you need to keep people away from hazardous areas or in situations where climbable objects might be used to bypass your existing security fence and gain access to restricted areas.
This aspect of security fencing is often overlooked but Australian workplace health and safety regulators require you to take steps to isolate work site hazards. Neglecting this aspect of site security could prove costly, for you, your company, and an intruder.
Unfortunately, many people tend to be a little blasé about security but if you are in charge of health and safety on your premises then you have a heavy responsibility to take unauthorised access to hazard areas seriously.
The particular nature of your site and its hazards may require an exclusion zone. An exclusion zone is a fenced off buffer area that is designed to prevent site security being bypassed in opportunistic ways.
Where might an exclusion zone be needed?
Sometimes the risk of unauthorised entry to restricted areas is too high and an exclusion zone is required. An exclusion zone is the first line of defence and prevents people from being able to make use of climbable objects or to use excessive force such as ram raids to bypass your security measures and gain entry to an area.
Some places where you may need a protected exclusion area:
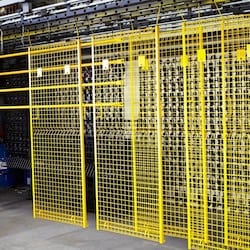
- Electrical substations
- Chemical storage areas
- Agricultural sprays storage areas
- Electric security fencing—where there is a risk to the public of accidental contact
A fenced exclusion zone is about preventing people from taking advantage of any opportunities to use climbable/movable objects nearby to get around your existing security fencing.
Why is my current security fencing inadequate?
Yes, you may have an existing well designed security fence but it may be inadequate in particular situations. Unfortunately, human nature remains the weak link in even the most well designed security system. It’s a little bit like the security on your computer; if you are careless and don’t update the antivirus programme you can lose everything.
In many cases of unauthorized entry it’s simply an opportunist seizing the possibility of using a load of pallets, a stack of timber, a container, a building roof or a tree to gain access.
You may have a company policy designed to prevent storage of goods next to the security area but human nature being what it is workers may forget in the stress of completing tasks or be under pressure for storage space. Or it could be a case of visiting contractors who, unaware of your company policy, unload their deliveries next to your security fence. It only takes one small slip for your site security to become vulnerable.
You also need to remember that some people will go to extraordinary lengths in an attempt to access restricted areas. It may be for the sheer challenge, for some kind of foolhardy dare or as a result of a drug induced state.
However, it is your job to plan for such possibilities.
A fenced off exclusion zone prevents objects being placed (accidentally or otherwise) in a position that would allow someone to bypass your existing security fencing. Exclusion zones reduce the impact of human error and remove the possibilities for slip-ups and opportunists.
What should I do?
You need to review your security regularly as small unnoticed changes may make a once secure site vulnerable. Never underestimate the lengths some people will go to gain access to your property and ask yourself, “could someone move that object and use it, or climb that tree, or get on to the roof and then gain access? What are the possible vulnerable areas in my site security?”
Health and safety regulators can impose severe penalties on site owners who do not do enough to protect employees and the public from site hazards. And there are a number of situations where you need to install exclusion zone security fencing.
Now would be a good time to review your site security and discuss your security needs with the helpful experts at Profence. We have the experts in security fencing and can offer a vast range of fencing options to suit all situations and requirements.
Look to Profence for the perfect security choice.
05/07/2017
Further reading: